There are two netctl-based commands which are run from the DataEngine
<cmd> listnetctl is-enabled <profile>Both of them do not require any additional privileges normally. Also DataEngine has two other command which will be run from; they should define external IP. According to the idea that user can set any command to run, this module is not secure. But running commands will not do more than user can do from console himself.
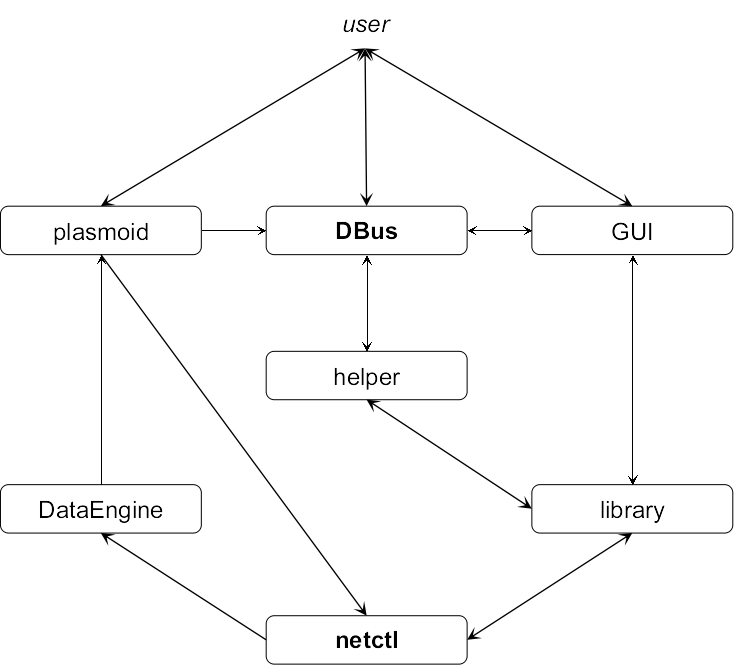
The widget gets information from DataEngine, thus it does not require any additional permissions to show information. But netctl calls with root privileges are used to control netctl. In this case used commands are
netctl enable <profile>netctl disable <profile>netctl restart <profile>netctl start <profile>netctl stop <profile>netctl switch-to <profile>netctl-auto switch-to <profile>All netctl-based commands requires root privileges and sudo (and any other alternatives) is used normally as prefix to the commands. The netctl-auto command does not require additional permissions.
The other way is to use DBus communication with the helper. In this case user should have rights to start the helper.
Graphical interface may interact with netctl over DBus (the helper) and over the library. Please refer to their notes to any additional information. If user uses helper he should have permissions to run it.
According to the scheme library gets information from netctl and can control it. Also it provides some additional functions such as a profile creation and removal and access to wpa_supplicant functions. Some function does not require additional permissions, but other ones do it. All dynamic arguments including profile names and paths are in double quotes to avoid white spaces problem. The functions which requires root privileges are:
netctl start|stop|restart|switch-to|enable|disable <profile>. They are commands which provide a general control to netctl.systemctl start|restart|enable <netctl-auto@service>. They are commands which provide ability to control netctl-auto systemd service.cp command is used for it.rm command is used for it.CTRL_GROUP.
© 2014-@CURRENT_YEAR@ @PROJECT_AUTHOR@
This software is licensed under @PROJECT_LICENSE@